100k Bot Graveyard Daily: Reddit’s Face-Tax Kills Anonymity
TL;DR
- Stately Taurus APT deploys USBFect malware and EggStremeFuel backdoor in Southeast Asian government cyberespionage campaign
- Ajax Amsterdam discloses cybersecurity breach exposing 538 season ticket holders' accounts via mobile app vulnerabilities
- Reddit implements non-human account labeling system, blocking 100,000 suspicious accounts daily with App labels and proof-of-personhood verification
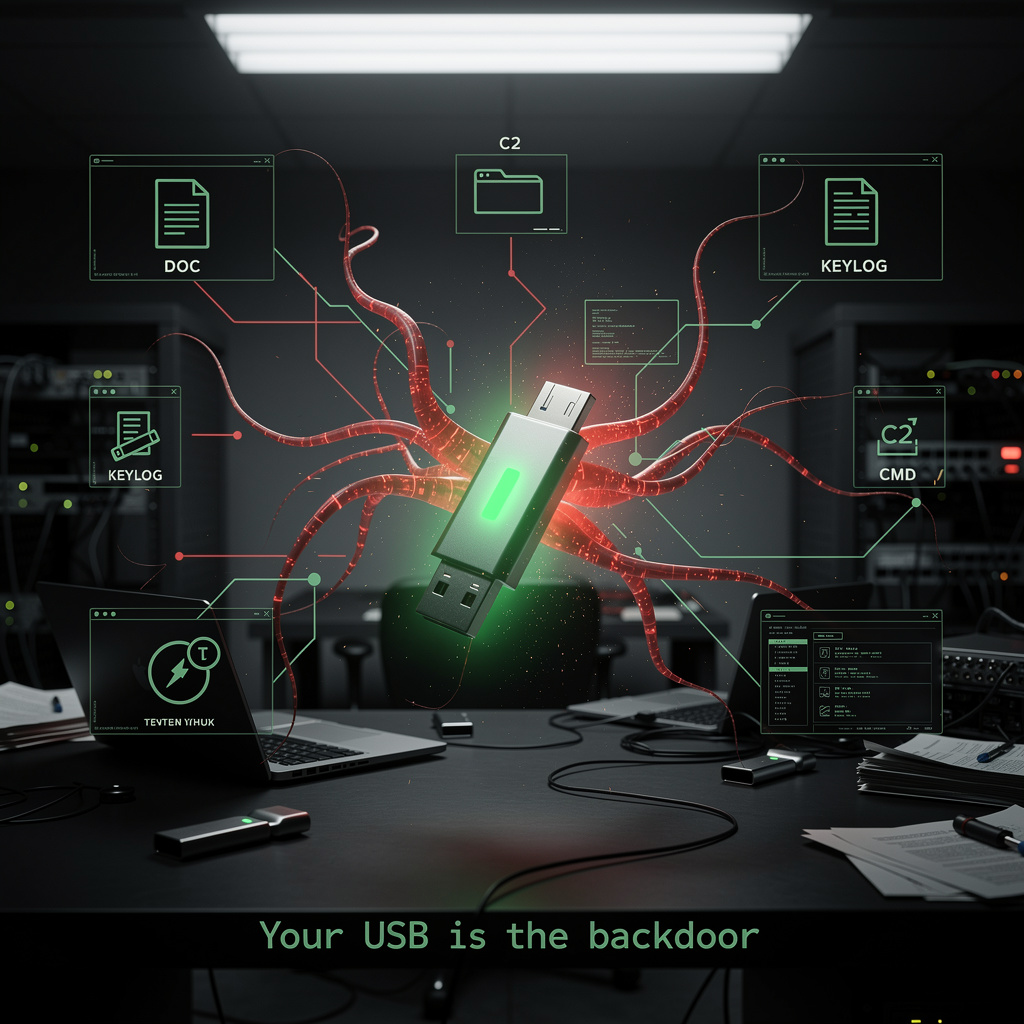
😈 90% Infection Rate: USB Spies Pillage SEA Ministries
90% of SEA gov PCs kissed a USB & woke up with spyware hangovers—keyloggers slurping passwords like free bar snacks 😈💾 Your tax dollars, their silent data rave. Kill autoplay or keep feeding the beast—how many ministries will admit they’re pwned?
Remember when the worst thing a USB stick could do was give you a 2004 mixtape you never asked for?
Stately Taurus just turned that nostalgia into a 75-day bloodletting: 90 % of sampled Southeast-Asian ministry boxes now host USBFect, an auto-run gremlin that clones itself the instant you plug in. Translation—every coffee-run flash drive is a potential government skeleton key. ☕💀
How the hell did a $4 dongle outfox million-dollar firewalls?
- Physical cheat code: No phishing link, no zero-click SMS—just “Here, Mr. Officer, print my docs.”
- File squatting: Drops EVENT.dll & UsbConfig.exe under ProgramData\intel_\ like it owns the place.
- Encrypted chit-chat: Abuse of CryptEnumOIDInfo API wraps C2 in vanilla TLS—your IDS thinks it’s just another Windows handshake.
- Persistence on a budget: ClaimLoader decrypts shellcode, EggStremeFuel keylogs creds, FluffyGh0st finishes the looting. All open-source modules, duct-taped by a guy who probably still lives on instant noodles.
Impacts—because numbers bruise harder than adjectives
- Dwell time: 75 days → long enough to memorize every password, budget draft, and petty e-mail feud.
- Re-infection runway: 4 distinct agent paths per victim → good luck scrubbing every forgotten laptop in the back office.
- Detection lag: Encrypted C2 keeps traffic looking “normal,” so analysts chasing APT flags are basically sniffing their own aftershave.
- Budget burn: Post-breach cleanup averages 6× the cost of simply disabling auto-run—something any intern could do with a registry tweak and a hangover.
Short / Mid / Long—mark your calendar, pop the anxiety
- Q2 2026: Detection signatures drop; 30 % of agencies still ignore “Disable USB” memos because, you know, convenience.
- 2027: Taurus ships v2 minus CryptEnumOIDInfo tells; infection rate dips 40 % only if orgs actually enforce code-signing for removable media (spoiler: most won’t).
- 2028: Expect modular, air-gap-hopping variant targeting power-grid lobbies—same cost (zero), new body count.
TL;DR for the corner office
Your “air-gapped” network is now only as thick as the nearest thumb drive. Disable auto-run, whitelabel firmware, or keep funding some hacker’s Steam library. Pick one—entropy’s already picked its side.
😂 538 Stadium Bans Erased: Ajax App Breach Hits 300k Fans
300k+ Ajax fans pwned by a mobile app held together with duct tape & wishful thinking—538 bans vanished faster than their title hopes 😂💥. No rate-limit, no auth, just vibes. Dutch DPA incoming, legal bills stacking. Fans: still paying €50/mo for the privilege of being beta-tested. Who’s next in the Eredivisie glitch lottery?
Ajax Amsterdam’s mobile app was supposed to make life easy for fans; instead it handed 538 of them a free stadium-ban lift and let at least one stranger waltz into the VIP section with a stolen season pass. Over 300 000 accounts—basically the entire digital grandstand—got caught in the cross-fire after crooks replayed login tokens and told the club’s APIs, “Yeah, sure, I own that ticket, un-ban my mate while you’re at it.” The club’s own SIEM logged 1.1 million malicious calls before anyone hit pause.
How did a football app become a free-for-all?
- No-owner check: the
/ticket/transferendpoint accepted any user ID you typed in. - No-role check: the
/ban/updateendpoint let you overwrite stadium bans without asking who you were. - No-rate limit: 538 ban edits and countless ticket swaps executed in seconds.
- Token replay: once you had a session cookie you could re-use it like a day-pass.
Impacts, in bite-size humiliation
- 538 fans: wrongful un-banning → potential crowd-trouble liability.
- One “Menno Geelen” ticket: reassigned to rando → VIP seat filled by stranger.
- 300 000+ users: forced app logout, 2.3.1 patch rammed down their throats.
- Ajax coffers: €5-10 k to reprint/validate tickets; reputational bruise broadcast from Amsterdam to ESPN.
- Regulators: GDPR fine-loader spinning; Dutch DPA now auditing for a low-six-figure penalty.
What they’ve duct-taped so far
Patched app, killed vulnerable endpoints, slapped on multi-factor auth, hired outside pen-testers, and cranked the rate-limiter to “annoying.” Translation: the digital equivalent of locking the barn door after the horse has already scored a hat-trick in someone else’s colours.
Timeline of looming fun
- Next 2 weeks: mandatory app update; expect grumpy boomers at the turnstiles.
- Q2 2026: GDPR verdict—expect a €100-200 k wrist-slap if regulators feel generous.
- 2027: Dutch Eredivisie clubs forced into OWASP-style security boot camp; third-party ID platforms bag the next ticketing contract, because nobody trusts in-house code anymore.
Final whistle
Ajax just proved that if you treat your back-end like a practice squad, hackers will still put eleven past you. For every club still running hobby-grade APIs: patch, limit, verify—or prepare to explain to 300 000 fans why their seat suddenly belongs to a guy in a balaclava.
🪦 Reddit Axes 100k Bots Daily, Demands Face-ID or Iris Scan for Human Badge
100k bot corpses/day 🪦—that’s a whole city of fake ‘users’ evaporating while you sip coffee. Reddit’s new robo-tag turns your burner alt into a glowing [APP] scarlet letter unless you cough up Face-ID or an iris-scan token. Anonymity? Nah, now it’s pay-to-play humanhood. So—ready to flash your eyeball for karma, or bailing to the dark-web forums?
Reddit just duct-taped a lie-detector to every bot’s face and yanked 100,000 digital corpses off the platform before breakfast. On 26 March the site flipped a switch: automated accounts now wear a scarlet “NON-HUMAN” badge, while devs who want their scripts to survive must beg for an “[APP]” stamp and, if the algo smells fish, whip out an iris-scan or Face ID. Result? A daily massacre of 100k sock-puppets—roughly the population of Reykjavík—evaporating in real time.
How the kill-box works
A behavior engine times your keystrokes like a jealous ex: post too fast, parrot the same meme, API-spike at 3 a.m. and you’re flagged. Humans can unlock with a passkey fingerprint; bots either register (and get tagged) or take the perma-ban hammer. World ID’s zero-knowledge iris token acts as a “meat-puppet coupon” no personal data ever touches Reddit’s disks—just a Boolean: meat = 1, metal = 0.
Impacts in one breath
- Spam: 15 % of all posts were AI slop → now projected 30 % drop in two weeks.
- Mods: 12 k legit bots already self-stamped, so janitors can finally ignore the good appliances.
- Privacy purists: biometric token optional everywhere except UK/AU where Uncle Sam’s cousin demands real ID—expect torches and pitchforks.
- Bot herders: evasion code will mimic human cadence; cat-and-mouse budget just became a line item.
Short / long torture schedule
- Next 90 days: block rate hovers at 95-105 k/day while algos binge on fresh evasion tactics.
- Late 2026: detection precision >90 %; daily body count drops to 70 k yet spam stays buried.
- 2027-28: decentralized ID cards replace eyeball scanners; Reddit becomes the first major platform where “anonymity” is opt-in, not birthright.
Bottom line
Anonymity is now conditional; play nice, verify your pulse, or join the 100k daily ghosts.
In Other News
- Microsoft releases Windows 11 26H1 with KB5083990, enforcing Secure Boot certificate renewal ahead of June 2026 expiry


Comments ()