$290M AI Anti-Phish Flunks Lunch-Order Test: US Firms Face 50 % Leak Odds
TL;DR
- Dataminr launches AI-powered CyberDefense suite integrating client-tailored threat intelligence with internal telemetry
- Proofpoint achieves 99.999% detection efficacy with unified email security platform for AI-driven agent threats
- Chinese hackers infiltrate Microsoft GCC cloud system, exposing DOJ data and triggering federal audit
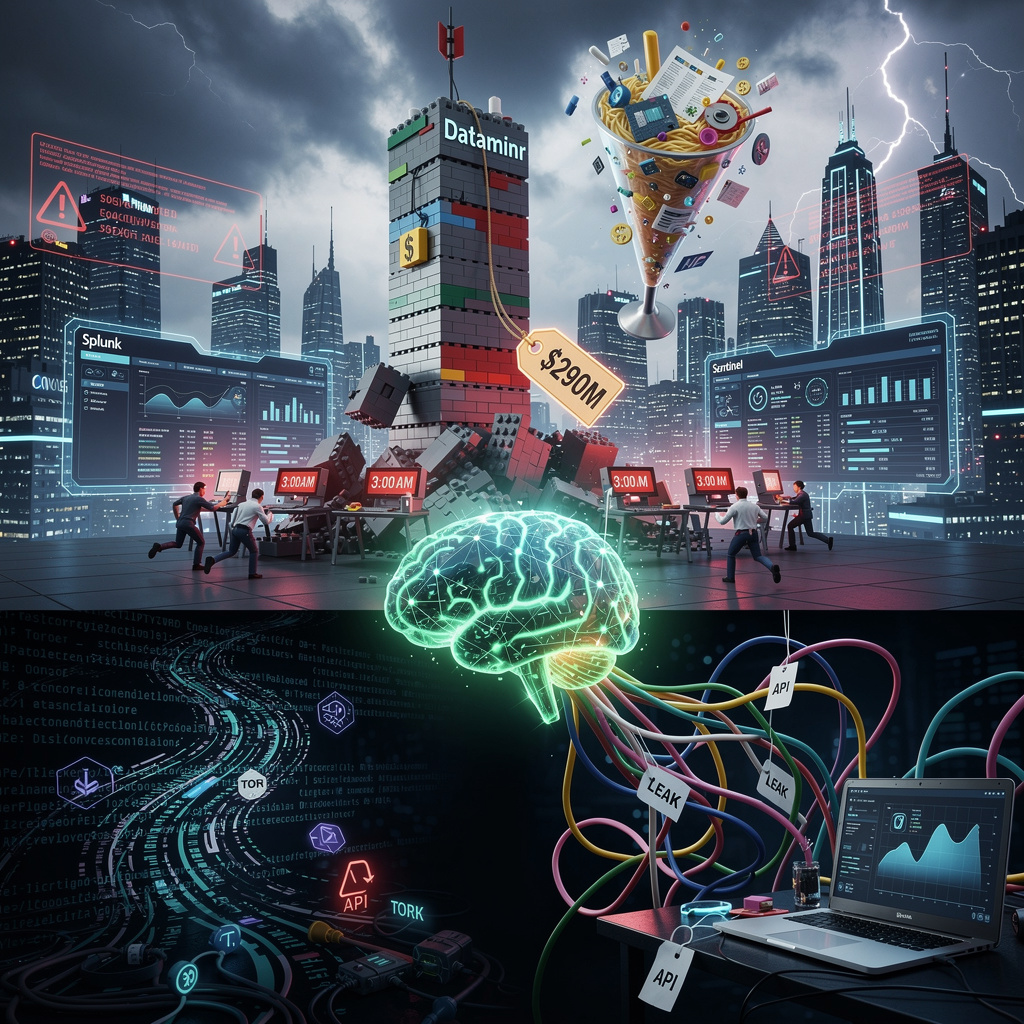
💸 $290M AI Cyber Suite Debuts at RSAC: 40% Faster Alerts, Same Legacy Headaches
$290M buys you 3 shiny AI bots that still can’t tell a phishing mail from your CFO’s lunch order 🙃 40% faster? Great—until the model hallucinates your payroll as ‘suspicious activity’ 💸 SOC analysts, meet your new overtime generator—who’s ready to beta-test on production finance data?
Dataminr drop-kicked its CyberDefense suite onto the RSA stage yesterday, gluing three buzzwords—Client-Tailored Intel, Agentic TI Ops, Continuous Exposure Management—into one very expensive Lego set. Price tag for the plastic: $290M (ThreatConnect) plus whatever your SIEM plumber charges to duct-tape it in.
How does this “fusion” taste?
- Slurps every RSS feed, Telegram channel, and dark-web postcard.
- Stirs in your own logs until the AI spits out a “risk milkshake.”
- Pings Splunk/Sentinel playbooks so the intern can click “Accept” faster.
Result: up to 40% less time from “uh-oh” to “meh,” says Gartner’s back-of-napkin math.
Impacts – the receipt
Analyst overtime: 15-20% cheaper → still not cheap enough to fund their therapy.
Competitive heat: CrowdStrike & Sentinel now race to glue the same LEGO before your budget freezes.
Integration hangover: heterogeneous legacy = API spaghetti → SIEM consultant’s kids go to private college.
False-positive roulette: model misfires → 3 a.m. page, again, because “everything is critical.”
Timeline of promised miracles
- Q2-Q4 2026: big banks pilot → 30 petabytes of logs, zero weekends.
- 2027: Gartner labels it “Strong Performer,” vendors copy-paste, prices drop 12%.
- 2028: Dataminr bolts on zero-trust autopilot; industry standardizes on yet another JSON schema nobody asked for.
Bottom line
Telemetry fusion is now table stakes; the only winners are vendors billing by the hour. Your choice: pay the ransomware or pay the platform—either way, the house always wins.
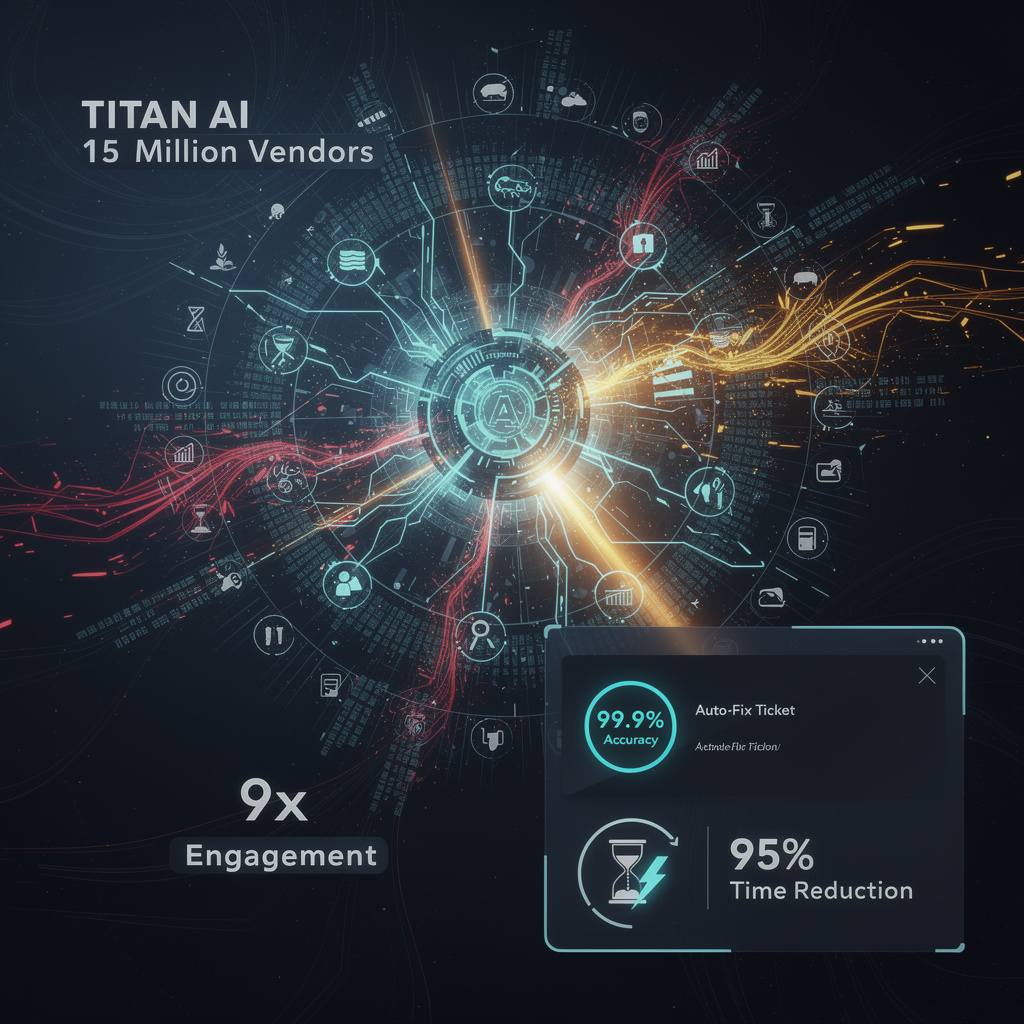
🎣 99.999 % Detection: Proofpoint Unifies SEG-API to Cage AI Email Agents
99.999 % catch-rate? That’s 1 phish in 10 million slipping through—odds better than your paycheck keeping up with inflation 😂. Proofpoint’s new robo-bouncer now frisks AI agents at the door, slashing breach busywork 70 %. But hey, if 50 % of firms still plan to leak data next year, who’s really winning? US IT peeps—ready to let a SaaS overlord babysit your bots, or still DIY with duct-tape & prayers?
Proofpoint’s new unified email shield claims 99.999 % catch-rate for AI-agent slime—think of it as a bouncer that never blinks while 24 trillion data points from 42 k companies whisper “punch list” in its ear. SEG + API tag-team north-south and east-west traffic, so the same malware that once lounged past the firewall now face-plants at the gate and again in the hallway.
How it actually works (no pixie dust)
- Intent-based engine chews every inbound, outbound, internal message.
- URL re-write + sandbox detonate clicks & attachments milliseconds after you’re tempted.
- Agent Integrity Framework demands ID before any AI bot can hit “send,” neutering zero-click prompt-injection.
- Single console auto-stomps stale credentials, trimming ticket grunt-work by 70 %.
Impacts—coffee-spitting edition
- BEC carnage: 3× more credential-phish caught, meaning your CFO won’t wire $500 k to “Dubious Vlad.”
- Inbox noise: –48 % phishing volume in 90 days—roughly 17 fewer garbage mails per employee per month.
- Analyst life: average triage collapses from 16 h to 5 h—goodbye midnight pizza.
Short-term bruises (next 12 mo)
- Q2 2026: connector army >350 vendors; cross-threat intel swaps like Pokémon cards.
- Q4 2026: NIST AI-agent rules loom—Proofpoint becomes the compliance cheat-code.
Long-term scars (24-36 mo)
- 2027-28: market folds into “unified-only” stacks; vendors without SEG+API combo become nostalgia acts.
- 2028-29: regulators slap agent-identity mandates on every outbound mail—late adopters pay lawyer vacations.
Bottom line
Email’s future is bot-on-bot violence; Proofpoint just handed enterprises a lead pipe. If your current gateway still thinks “internal” equals “safe,” start budgeting for breach apologies—or buy the upgrade and let the robots fight it out while humans stay blessedly ignored.
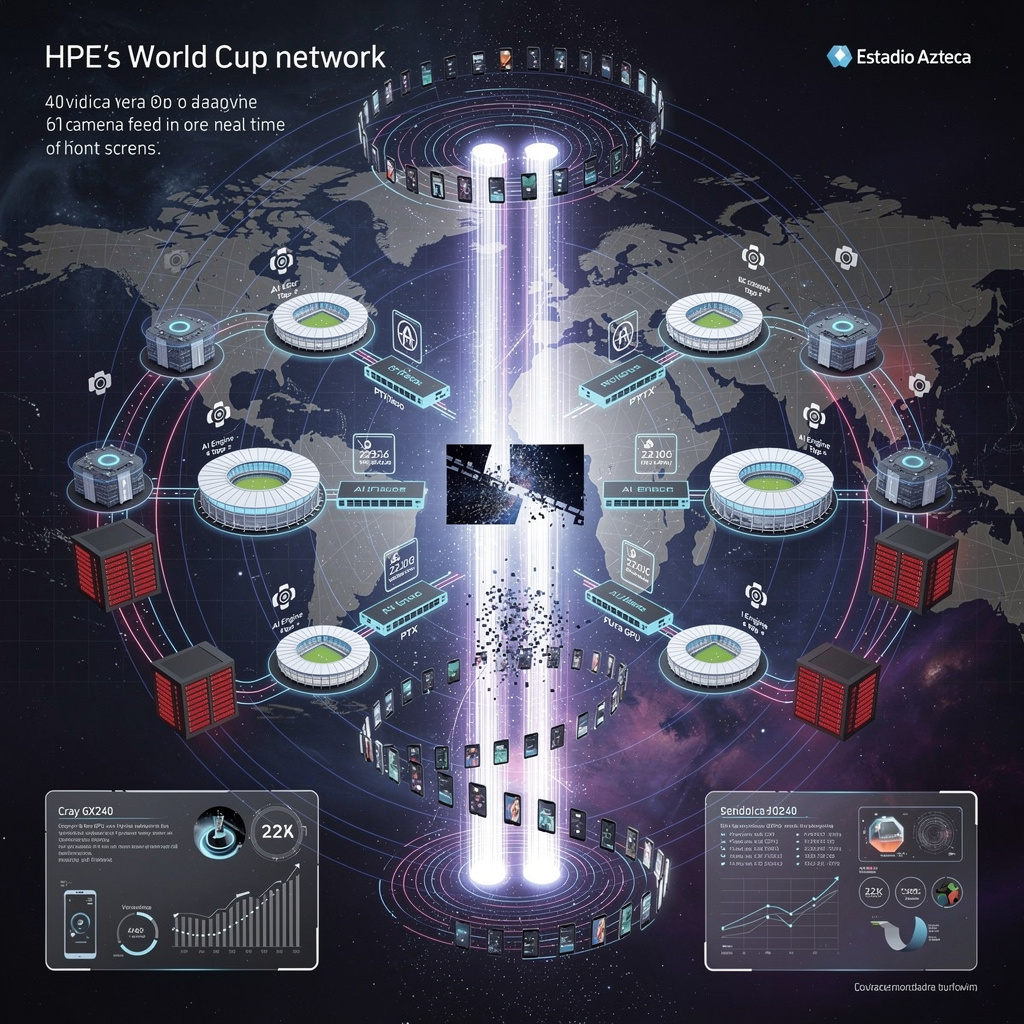
🤡 $1B DOJ Breach: China Looted Microsoft GCC-High Amid FedRAMP Chaos
$1B DOJ data heist—China read your Gmail before you did 😂 50% FedRAMP budget gone, 5-yr auth limbo, still no real crypto docs. Tax-funded clown car 🎪—your jury files, their Git commit. Who’s upgrading to ‘Made-in-USA’ cloud before the next snoop?
Chinese keyboard cowboys just looted the Justice Department’s “super-secure” Microsoft cloud like it was a dorm fridge at 2 a.m.
Result: $1 billion of taxpayer secrets flapping in the Beijing breeze and FedRAMP auditors slamming the brakes on the whole GCC-High circus.
How the heist went down
The DOJ CIO—who later parachuted into a Microsoft gig—green-lit the move in 2020.
By 2023, Chinese APT crews were roaming senior e-mail accounts; they didn’t even need ransomware—just grabbed the attachments and ghosted.
Microsoft’s security paperwork? A cocktail-napkin doodle: no data-flow maps, no key-management nitty-gritty, and—chef’s kiss—China-based engineers doing nightly maintenance on the very servers U.S. policy bans them from touching.
Impacts—bullet-point bruises
- Data: every DOJ case file, procurement record, and Cabinet e-mail now cloned in some Shenzhen hard-drive zoo.
- Cash: $1 billion exposure—enough to fund the entire FedRAMP program for a century, now vaporized in remediation and lost-contract penalties.
- Credibility: auditors slapped a “buyer beware” sticker on GCC-High; authorization frozen through 2026 while Microsoft plays 200-page Mad Libs with security docs.
- Careers: former DOJ brass caught rubber-stamping the bypass; Accenture staffer indicted for FedRAMP fraud; Microsoft still billing by the hour.
Outlook—three horizons of schadenfreude
- Next 12 months: Microsoft must exile every non-U.S. engineer and dump a paper mountain on auditors’ desks; DOJ may yank contracts anyway.
- 2027: new Fed rule—zero foreign hands on federal cloud; budget doubles to $20 million so reviewers can stop playing whack-a-mole.
- 2028–29: expect a Made-in-USA cloud cartel and hybrid on-prem stacks for anything juicier than a parking ticket.
Bottom line
The breach proves “government-grade” is just marketing glitter. Until the feds treat cloud security like launch codes—not license fees—every agency inbox remains a free-fire zone for whichever nation-state loads Metasploit first.
In Other News
- Microsoft rethinks Windows 11 mandatory Microsoft account requirement amid internal and user pressure
- CanisterWorm malware campaign targets npm ecosystem, deploys destructive payload wiping systems configured for Iran's timezone
- US DOJ seizes four Iranian MOIS-operated websites and offers $250K bounty for targeting Goldie Ghamari
- VoidStealer malware exploits Chrome's Application-Bound Encryption to steal authentication tokens

Comments ()