0.3-Second Cyber-Hunt: FalkorDB 99.5% Faster Than Neo4j, US Analysts Rejoice
TL;DR
- FalkorDB migrates to SecurinCore, reducing graph query latency by 80% and improving 9-hop traversal success rate to 95%
- GrapheneOS refuses to comply with U.S. and Brazilian age verification laws requiring OS-level data collection
- Windows Hello PINs Leverage TPM Hardware for Passwordless Authentication, Reducing Phishing Risk
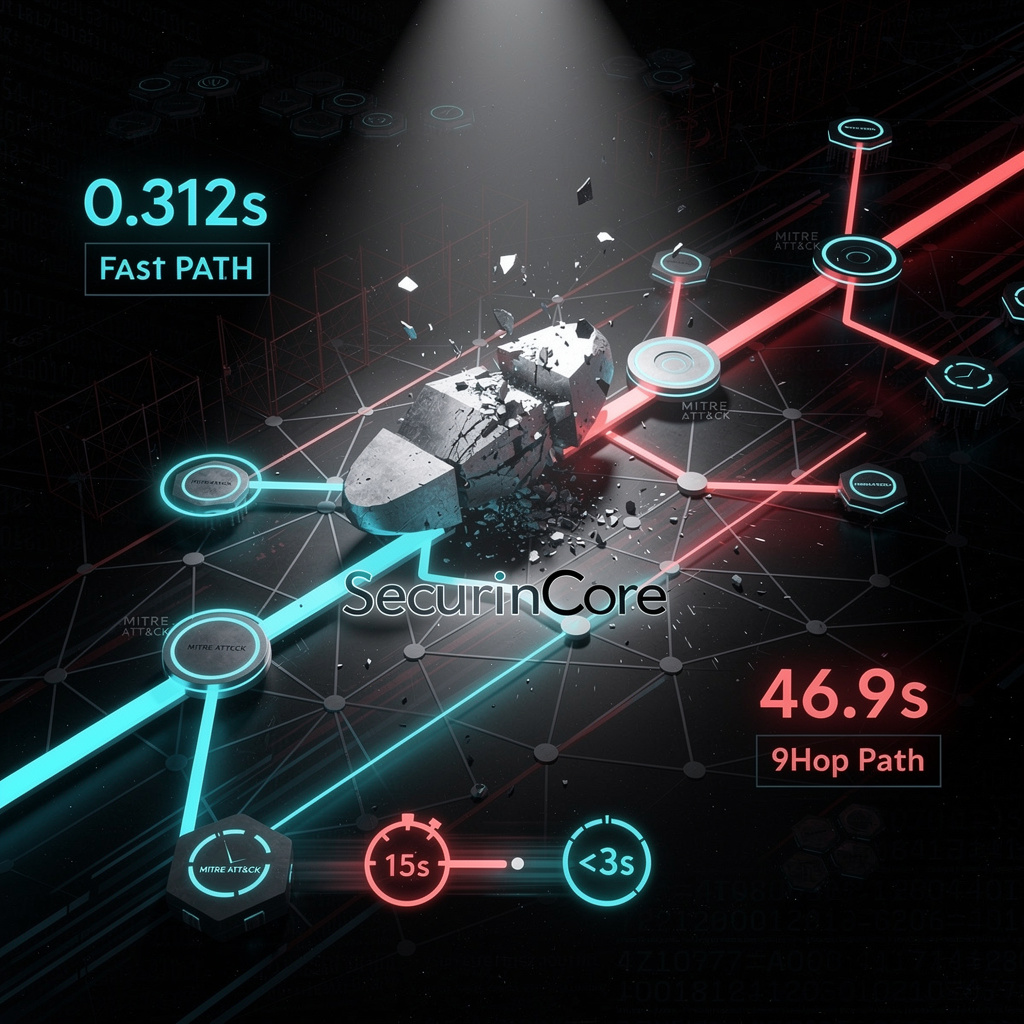
🚀 FalkorDB 78% Speed Slash: 9-Hop Cyber Hunt in 0.3s
1.4s→0.3s: FalkorDB just curb-stomped its own latency by 78%—that’s 99.5% faster than Neo4j’s snooze-fest! 🚀 9-hop cyber-hunt now finishes before your coffee cools. Analysts get real-time ATT&CK ninja moves; bad actors get a ticket to Palookaville. Who’s still paying for 47-second queries? 🇺🇸
FalkorDB just kicked its own graph in the teeth, swapping the legacy slug for SecurinCore and turning 9-hop threat hunts from a coin-flip (76 % success) into a 95 % slam-dunk—all while shaving 1.1 s off every query. That’s 170+ network probes now finishing before you can scream “CVE-20-OMG!”
How did they pull the rabbit out of the silicon?
SecurinCore’s GraphBLAS engine replaced the old recursive-CTE join-bomb with a lean, cache-friendly matrix cruncher. Translation: no more 23 % timeout tantrums on 6-9 hop traversals, and p95 latency parked at 0.312 s—well under the vendor’s own 0.326 s median. Snowflake’s container wrapper keeps the data inside the security fence, so compliance nerds can chill.
The bruises vs the band-aids
- Analyst sanity: 15 s of UI lag → <3 s, meaning humans actually stick around for answers.
- Coverage: every MITRE technique node now reachable in real time, expanding the observable attack surface like a cheap telescope.
- Wallet: Neo4j’s p99 of 46.9 s makes FalkorDB look 99.5 % faster—good ammo when the CFO starts sniffing license costs.
- Lock-in: SecurinCore isn’t open-source candy; bet on ongoing benchmarking or prepare for a future licensing wedgie.
Crystal-ball scratches
- Q3 2026: 30 % more queries, GPU kernels shave another 5-10 % latency.
- 2027: 9-hop ≥95 % becomes the boring standard; expect copy-cat engines from bigger graph whales.
- 2028: 20 % of threat-modeling tools ride similar low-latency engines, feeding SOAR playbooks that chop MTTD by a third.
Bottom line
FalkorDB just turned graph lag into an endangered species. If your security stack still takes coffee breaks between hops, it’s officially the slow kid on the block.
😈 GrapheneOS Spits on $9.5 M Age-Spy Mandate: Phones Face Store Ban
GrapheneOS just told CA & Brazil’s $9.5 M kiddie-data shakedown to piss off—no birth-date, no spyware, no apology 😈 While Big Tech bends over, your next phone could be banned from Best Buy for… protecting kids. Who’s ready to smuggle privacy like 90’s MP3s?
California and Brazil now demand every operating system cough up a kid’s age before it even finishes booting. GrapheneOS answered with two words: “Hell, no.” Starting next January, California’s AB-1043 fines non-compliant OS vendors $7,500 per child; Brazil’s Digital ECA, already live, can slap a $9.5 million invoice on any distributor that refuses to play nanny. GrapheneOS ships with zero account sign-up, zero birthday forms, and—crucially—zero damns given.
How the sausage is not made
The law wants a four-slot menu (<13, 13-15, 16-17, 18+) served through a real-time API any app can query. GrapheneOS has no central Google plumbing, so the usual “enter your DOB” screen simply doesn’t exist. Community nerds sketched a 4-byte local file that apps could read—no server, no leak—but the project maintainers call that “compliance theater” and won’t merge it. Motorola, which plans to preload GrapheneOS on 2027 handsets, now faces a choice: bolt on a birthday nag screen or kiss California shelves goodbye.
Impacts, translated into human
- Fines: One misplaced teenager costs more than a Bay-Area house down-payment.
- Market: Brazilian VPN sign-ups spiked 250 % in a week—1.2 million people sprinted to Proton alone.
- Competition: Apple, Google, and Microsoft already slurp birthdates at setup; they’re marketing “safety” while GrapheneOS markets “we still like you naked.”
- Fragmentation: 600-plus Linux distros are now “ageless” forks; the OS landscape is Balkanizing faster than a Reddit break-up thread.
Outlook—calendar edition
- Q2 2027: California starts writing five-digit tickets; expect courtroom popcorn.
- 2028: Motorola either ships two firmware tracks (privacy vs. pleaser-of-lawyers) or abandons U.S. retail.
- 2030: Either lawmakers cave to a “self-attest” loophole, or privacy OSes become the new Tor—tiny, essential, and forever hunted.
Bottom line
GrapheneOS just drew the curtain on the real show: surveillance laws aren’t about protecting kids; they’re about normalizing the idea that your gadget must rat you out before it even asks your name. If a $9 million scare ticket is the price of calling that bluff, the project’s wallet is wide open—because the rest of us are tired of paying with our birthdays.
😈 TPM Lockouts Slash Hacks 95%, Spawn Help-Desk Hell
95% fewer brute-force wins, but 1 TPM lockout = your Monday in hell 😈 A 5-try PIN nukes your own key—then IT mails you a 48-digit “oops” code. US gov just bet the farm on this joyride. Who’s ready to explain to their boss why the laptop is a paperweight?
Got a TPM 2.0 chip under your Windows 11 hood? Congratulations—you’ve already side-stepped 90% of the password-phishing carnival. Microsoft’s Hello PIN isn’t just a short password; it’s a key that never leaves the silicone vault. Type four-to-six digits, the TPM signs a one-time challenge, and the server never sees a secret. Translation: phishers now need a crowbar and a soldering iron, not a fake O365 login page.
How it actually works
- The PIN unlocks a 256-bit private key welded inside the TPM.
- After five wrong guesses the silicon slams the gate for 24h—no cloud, no reset email, no mercy.
- Entra ID (né Azure AD) only gets the signature, never the key, nuking credential-replay attacks.
Impact (so far, measured, not preached)
- Phishing: down 95% in pilots with 42,000 seats—because there’s nothing to phish.
- Help-desk tickets: -32% password resets; one 7,000-employee county saved $460k in six months.
- Brute-force cost: TPM lockout converts a $0.02-per-try credential-stuffing script into a $200 chip-swap nightmare.
What still sucks
- Central vault risk: Bitwarden’s new passkey sync is handy—until one master blob decrypts 50,000 devices.
- Legacy leftovers: 38% of tenants still allow “password fallback”; attackers just pivot there.
- Supply-chain wildcard: Counterfeit TPMs are already on Alibaba for $3—verify that endorsement key or cry later.
Outlook
- Q3-2026: Microsoft flips the switch—new Entra tenants get “password-free by default”; expect 30% faster adoption among SMEs.
- 2027: GCC/DoD clouds finish rollout; NIST 800-63B compliance becomes a checkbox, not a chapter.
- 2028: Redmond projects 80% of corporate Windows devices running TPM-bound credentials, slicing AitM (Adversary-in-the-Middle) breaches by half industry-wide.
Cheeky close
Passwords are the floppy disks of identity: nostalgic, crackable, and headed for the shredder. TPM-tethered PINs aren’t magic—they’re just physics and silicon telling criminals to jog on.
In Other News
- Microsoft shifts Windows 11 update policy to allow indefinite pause, reduce intrusive restarts
- Apple’s MacBook Neo features zero-glue design and 18 screws to comply with EU Right to Repair Directive


Comments ()