VB6 Malware Beats $100K EDR: Legacy Code Is Now 'Advanced Evasion'
TL;DR
- DarkCloud infostealer malware targets enterprise credentials via browsers and email clients, marketed as surveillance software with VB6-based evasion
- ResidentBat malware targets Belarusian authorities with C2 infrastructure in Netherlands, Germany, and Switzerland, using port range 7000-7257
- iOS 26 and iPadOS 26 Certified by BSI for NATO Classified Networks, First Consumer Devices Approved
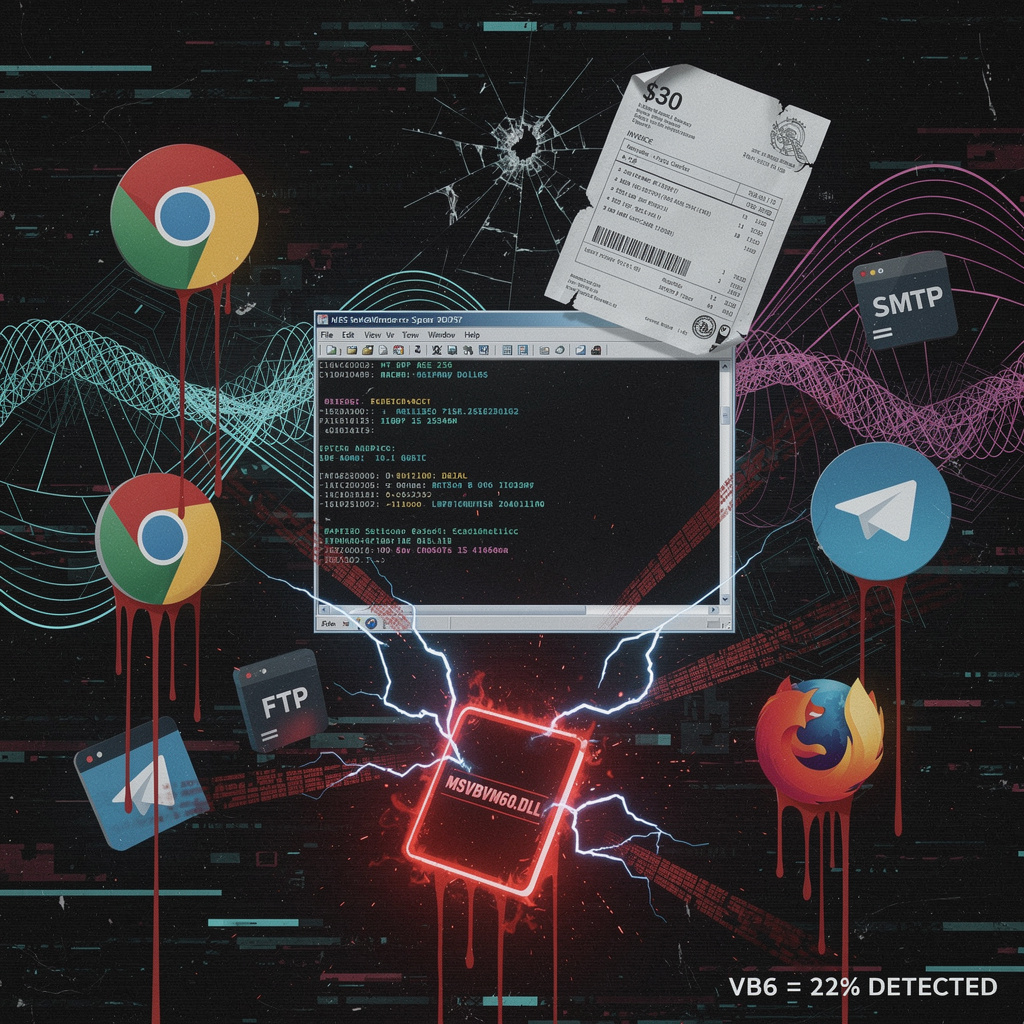
🫠 DarkCloud: 22% Detection Rate, VB6 Malware Bypasses Modern EDR in Enterprise Breach Wave
22% detection rate. VB6. In 2026. 🫠 Your $30/month "surveillance software" just outsmarted six-figure EDR budgets. DarkCloud's slinging stolen credentials via SMTP like it's 1999—because legacy bloat is now elite evasion. 15GB of passwords per 10k machines, funneled through Telegram bots and Azure instances your SOC pays for. The real zero-day? Microsoft's own signed DLLs becoming malware infrastructure. CISOs blocking MSVBVM60.DLL yet, or still explaining to boards why 'defense in depth' means praying? — What's the most embarrassing legacy tech still running in YOUR stack?
DarkCloud infostealer landed in late February 2026 with all the subtlety of a VB6 runtime error—except this one actually works. For thirty bucks a month, any script-kiddie with a forum account can harvest enterprise credentials from Chrome, Edge, Firefox, Outlook, VPN apps, and whatever else your users clicked "remember password" on. The punchline? It's compiled in Visual Basic 6, a language older than half your security team's careers, and that's precisely why it slips past detection.
How does this even function in 2026?
Two delivery variants exist. The primary VB6 build leverages MSVBVM60.DLL—signed, generic, utterly unremarkable to signature-based tools. A secondary C/C++ payload from the Lightningbytes toolkit shares the same pseudo-random generator for deterministic staging. Harvested data lands in %APPDATA%\Microsoft\Windows\Templates as raw databases, then exits via SMTP, FTP, HTTP, or Telegram bot API—operator's choice. AES-256 encryption wraps the payload before transmission, because apparently even budget malware needs standards.
What the numbers actually reveal
- Detection collapse: 22% catch rate for VB6 variant versus 58% for C/C++—your AV is literally worse against code from 1998
- Scale: ~15 GB of credential data per 10,000 infected hosts at 1.3 MB average exfiltration
- EDR salvation: 35% detection uplift with behavioral heuristics—memory-based anomaly detection isn't optional, it's survival
- Code theft: 68% similarity to BluStealer, because why write new malware when Ctrl+C exists
Why your enterprise defenses are losing to shareware
Legacy runtime exploitation: VB6 binaries carry Microsoft certificates that static analysis treats as "probably fine"—your sandbox never had a chance.
Egress channel buffet: SMTP, FTP, Telegram—pick your poison, all standard protocols your firewall permits because "business needs."
Subscription economics: $30/month includes build pipelines and C2 templates. At that price, DarkCloud costs less than your coffee budget and compromises more than your annual penetration test.
Detection architecture failure: Organizations running signature-only AV face a 36-percentage-point gap between variants. The malware isn't sophisticated; your detection strategy is just old enough to vote.
Timeline: the slow-motion disaster you're funding
- Feb–Apr 2026: VB6 and PowerShell variants proliferate; macOS Chromium modules emerge as cross-platform expansion accelerates
- Q3 2026: OAuth token and API key harvesting replaces password theft as credential-reuse policies harden; same C2 channels, juicier targets
- 2027: AI-assisted toolkit integration surfaces—prompt-injection techniques embedding credential theft in generative-AI pipelines, because of course they will
The fix that costs less than the breach
Block MSVBVM60.DLL execution on endpoints without legacy VB6 applications. Restrict outbound SMTP/FTP/Telegram from workstations. Flag mass file writes to that Templates directory and abnormal encryption-API calls. Implement continuous breach-aware password filtering against the 5.4 billion known-compromised credential dataset. Feed observed C2 infrastructure to ISACs.
DarkCloud isn't an advanced persistent threat. It's a $30 reminder that your detection stack prioritizes marketing slides over actual runtime behavior. The VB6 evasion isn't clever—it's just older than your vendor's threat intelligence feed.
🦇 ResidentBat: Belarusian KGB Malware Hijacks EU Servers for 28-Device Surveillance Campaign
28 phones, 12 ministries, 1 malware family—and your tax dollars are hosting the C2 servers. ResidentBat's Belarusian KGB surveillance op runs on Dutch, German & Swiss infrastructure like a cheap VPS sale. 🦇 No CVE needed when you can just abuse legitimate APIs and call it 'advanced persistent threat.' Meanwhile EU diplomats probably have the same ports open for 'legacy applications.' Who's auditing YOUR hosting provider's clientele—Belarusian spooks or just crypto miners?
Here we go again. Belarusian KGB operatives—yes, that KGB, they kept the name because subtlety died in 1991—are running a digital surveillance racket out of Dutch, German, and Swiss servers like it's a perfectly normal side hustle. ResidentBat, first spotted in December 2025 by journalists who apparently have more cybersecurity chops than half the EU's CERT teams, now commands ten active C2 hosts. Five in the Netherlands. Two each in Germany and Switzerland. One lonely node in Russia, probably wondering why it didn't get the EU visa.
The technical guts? Depressingly competent. Windows and Android persistence via registry keys and device-admin enrollment. Encrypted TCP streams over ports 7000-7257—because nothing screams "legitimate traffic" like a fixed 257-port range for your spy operation. AES-256-CBC with a static IV, because even authoritarian malware devs cut corners. UPX packing, anti-debug checks, LZMA compression. It's not fancy. It's workmanlike. Which is worse.
Targets: 12 Belarusian ministries, 28 mobile devices, opposition activists' GPS logs and contact lists.
Attribution: Code comments literally contain "КГБ". Not a red flag. A red banner with hammer and sickle.
How This Actually Works
Spear-phishing or supply-chain compromise drops the payload. Registry Run keys and scheduled tasks maintain Windows persistence. Android enrollment hijacks device-admin privileges. Data—documents, keystrokes, locations, SMS—gets LZMA-compressed, AES-encrypted, and shipped to those EU-based C2 nodes. Egress filtering? Optional, apparently.
What Gets Broken
- Operational Security: 28+ devices confirmed compromised → ongoing intelligence exposure and activist endangerment
- Institutional Trust: EU hosting infrastructure weaponized for foreign surveillance → regulatory and diplomatic friction
- Attribution Confidence: High — Cyrillic operator notes, KGB campaign overlap, and the operational elegance of a state budget
The Response (Such As It Is)
Network blocks on 7000-7257. IDS signatures for packet headers. AppLocker whitelisting. The usual suspects—national CERTs, sector ISACs—getting IOC feeds they probably already had. No coordinated takedown mentioned. No hosting provider accountability. Just recommendations and thoughts and prayers for Belarusian civil society.
What's Coming
- 2026 (Q1-Q2): C2 expansion to additional EU cloud VMs; port-hopping within 7000-7257 to dodge lazy firewall rules
- Late 2026: Module integration with other KGB tools; probable targeting of EU diplomatic networks
- 2027-2028: Migration to TLS/443 for traffic blending; supply-chain compromise of third-party libraries for initial access
The Real Punchline
ResidentBat isn't sophisticated. It's persistent. It exploits the gap between "we noticed" and "we acted"—a gap measured in months, not hours, because European hosting providers still treat "customer" as a legal category rather than an operational assessment. The malware sits on AS20940, AS3320, AS33820. Real ISPs. Real infrastructure. Real failure of due diligence.
The Belarusian opposition doesn't need better firewalls. They need European regulators who treat foreign intelligence C2 nodes with the same urgency they reserve for GDPR paperwork. Until then? Static IVs and all, this operation keeps running.
🍎 NATO Clears iOS 26 for Classified Ops: Consumer iPhones Now Military-Grade
250M+ iPhones just got NATO's stamp of approval for classified docs—because nothing says "military-grade security" like a $999 consumer toy with a fruit logo 🍎 BSI certified iOS 26 for Restricted-level intel, no custom hardening required. Your tax dollars: now compatible with AirDrop. Meanwhile Android OEMs scrambling to explain why their "enterprise security" needed 47 third-party vendors and a prayer — which NATO member's procurement team is sweating the most right now?
Apple just convinced NATO that an iPhone is tougher than a bunker. The German BSI certified iOS 26 and iPadOS 26 for Restricted-level classified data—the first consumer devices ever cleared for NATO operational use. No custom hardware. No government-grade Franken-OS. Just your standard iPhone, now officially spy-worthy.
How does this work?
BSI validated six hardware-anchored controls: AES-256 GCM encryption, Face ID with Secure Enclave processing, Memory Integrity Enforcement with real-time kernel signing, immutable secure boot chains, Lockdown Mode for runtime isolation, and a fused hardware root of trust. These aren't software patches slapped on later. They're silicon-deep, baked in at manufacture.
Operational: ~250 million existing European Apple devices already qualify. NATO personnel can now BYOD into coalition environments without lugging separate secure bricks.
Financial: Eliminates custom hardware procurement and slashes training overhead—defense budgets breathe easier.
Geopolitical: 32 NATO nations now share one mobile security baseline. Germany and the US lead field deployment of iPhone 16 Series and iPad Pro M5 units.
What could still go wrong?
| Zero-day exposure | Post-certification Secure Enclave bugs → joint BSI-Apple CVE monitoring with rapid patch cadence. |
| User misconfiguration | Disabling Face ID or Lockdown Mode → mandatory MDM policy locks for NATO-classified use. |
| Supply-chain tampering | Third-party firmware injection → hardware root of trust with BSI-verified attestations. |
| Legacy incompatibility | Older NATO crypto suites → SDKs provided for Type-1 encryption module integration. |
Timeline
- 2026–2027: Phased rollout across German and US NATO units; IA guidelines revised to codify "Apple Certified Mobile Devices."
- 2027–2028: BSI evaluates iOS 27 for Confidential/Secret levels; rival Android OEMs scramble for comparable certifications.
- 2028–2031: Potential diversification push—hybrid solutions with NATO-issued secure peripherals to reduce single-vendor dependency.
The bottom line
Consumer tech just ate defense contracting's lunch. Apple proved that mass-market silicon, properly architected, outperforms bespoke military hardware on security economics. NATO gets mobility without compromise. Competitors get a homework assignment. And everyone else gets to wonder why their classified data needed a $5,000 ruggedized brick when a $999 phone does the job.
In Other News
- Samsung Galaxy S26 series introduces per-pixel polarizing filters and app-specific notification blackout

Comments ()