Medusa Ransomware: North Korea's $15M Hospital Shakedown
TL;DR
- Lazarus Group deploys Medusa ransomware against U.S. healthcare and Middle East targets, leveraging Blindingcan and ChromeStealer
- ShinyHunters breach CarGurus, compromising 12.6 million accounts with personal data including addresses and phone numbers
- CISA mandates federal agencies to inventory and decommission unsupported edge devices within 90 days under BOD 26-02
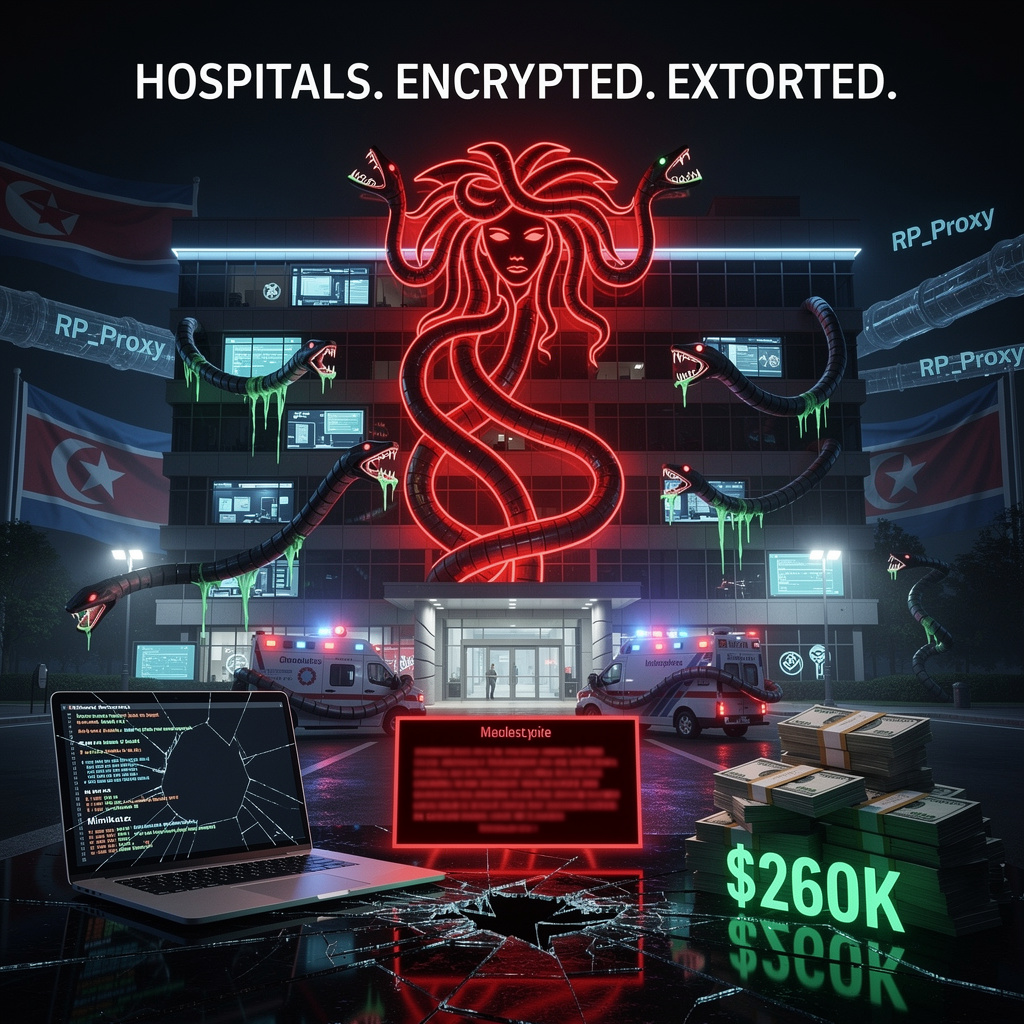
💀 North Korean State Hackers Ransom 300+ Hospitals: $260K Average, $15M Peak Demands
300+ hospitals ransomed by a government—not randos in hoodies. Lazarus's Medusa hits $260k avg, peaks at $15M 'sanctions' 💀 That's not cybercrime, that's state-sponsored bill collection. Your MRI machine? Funding North Korean nukes. Who's auditing your npm packages?
North Korean hackers—yes, that North Korea—have been running a ransomware side hustle since 2021, and U.S. healthcare is their ATM. Lazarus Group, Pyongyang's elite cyber unit, now deploys Medusa ransomware through a franchise model: affiliates break in, they encrypt, everyone splits the loot. Average take per victim? $260,000. That's roughly five years of a nurse's salary—gone in a weekend of encryption.
How the sausage gets poisoned
The attack chain reads like a sadistic recipe. Blindingcan and Comebacker backdoors establish persistence. ChromeStealer and Mimikatz vacuum credentials—browser passwords, domain hashes, everything. RP_Proxy tunnels stolen data through your own infrastructure, because why pay for bandwidth when you can steal the victim's? Finally Medusa locks files with AES-256, slaps on a .medusa extension, and drops a ransom note.
Initial access? Phishing dressed as job offers, or poisoned open-source packages like graphalgo on npm/PyPI. Your developer runs npm install, Lazarus runs your network.
What hurts, and how much
- Patient care: Encrypted EMRs, canceled procedures, ambulances diverted—operational paralysis measured in lives, not dollars
- Regulatory exposure: HIPAA violations, breach notifications, forensic costs stacking atop the ransom demand
- Financial bleed: $260K average demand; high-value targets hit with "sanctions" up to $15 million—extortion as foreign revenue policy
Over 300 organizations since 2021. Eighty-plus since February 2025 alone. Four currently listed on Medusa's leak site, their data held hostage in public.
The fix that isn't happening
Security teams should be: blocking known Lazarus C2 ranges, enforcing LSASS protection, whitelisting SMB/WinRM, auditing npm/PyPI packages, and—radical thought—testing backups quarterly.
What's actually happening? Underfunded hospital IT, legacy Windows systems, and developers who pip install whatever StackOverflow suggests. The tooling exists. The budget and attention do not.
Timeline: the pain ahead
- 2025–2026: Continued healthcare targeting; affiliates exploiting fresh Windows driver CVEs to blind EDR
- 2027–2028: Medusa evolves "double-extortion"—automatic data leaks, cloud EMR platform targeting, supply-chain infections chaining directly to ransomware deployment
The bottom line
Lazarus isn't just stealing money. They're stress-testing whether critical infrastructure can afford security. The answer, repeatedly, is no—and Pyongyang's counting on it. 🏥💸
🎣 12.6M Accounts Breached: Vishing Bypasses CarGurus' Cloud Security
12.6 million CarGurus accounts—just vishing. That's it. A phone call. "Hey, update your MFA." Boom. 431k unique emails, names, addresses, phone numbers, all because Dave from IT picked up the phone. 🎣 ShinyHunters didn't even break a sweat; they just asked nicely. Meanwhile your CISO's out here buying $50k "zero-trust" platforms that crumble to a voice call. CarMax, Panera, now this—same playbook, same clowns, same corporate "we take security seriously" blog post incoming. Who's next: your dentist's SaaS stack? — How many of your vendors would fold to one convincing phone call?
Oh look, another Tuesday in enterprise security—where your car-buying data takes a scenic detour through criminal infrastructure because someone picked up a phone. CarGurus just fed 12.6 million Americans to ShinyHunters, and the kicker? It started with a phone call. Not a zero-day. Not a supply-chain nightmare. A vishing campaign. Your MFA, that sacred totem of corporate compliance? Bypassed by social engineering so basic it hurts.
How does this even work?
ShinyHunters impersonated IT staff, convinced employees to "update" their MFA settings, then relayed credentials in real-time to seize SSO portals—Okta, Microsoft Entra, Google Workspace. From there, they harvested OAuth tokens via device-code flows, hit Salesforce and friends, and exfiltrated 6.1 GB of compressed PII. Admin access → API abuse → bulk export. No malware required. Just patience and a phone voice.
What actually got exposed
- Privacy: 12.6 million records dumped—names, emails, phones, home addresses → credential stuffing, targeted phishing, physical stalking risk
- Financial: $5M–$15M estimated hit for CarGurus in remediation, legal fees, and trust erosion
- Regulatory: State breach laws triggered; GDPR exposure for any EU users; California disclosure mandatory
- Supply-chain: Ancillary Salesforce records from Workday, DocuSign potentially swept up in the same grab
Where the defenses failed
| Control | Gap |
|---|---|
| MFA implementation | Push-notification fatigue exploited; no hardware-token enforcement |
| SSO monitoring | No anomaly detection on token issuance or bulk API exports |
| Employee training | Vishing simulation apparently optional until after breach |
| Vendor governance | Salesforce admin scopes too broad; no least-privilege segmentation |
What's coming next
- Immediate (days): Full 6.1 GB archive hits dark-web markets; credential-theft campaigns spike
- 0–3 months: Secondary extortion demands likely for "non-public" financial data from CarGurus' lending services
- 6–12 months: AI voice deepfakes enter the vishing playbook; ShinyHunters targets more SaaS identity providers for multi-tenant breaches
The bottom line
This breach isn't technically sophisticated—it's operationally inevitable. When your security model assumes employees won't answer phones, you're not doing security, you're performing compliance theater. The automotive sector, already bleeding from CarMax, now faces a pattern: cloud SSOs are the new soft underbelly, and vishing is the cheap drill.
Fix the human layer or keep feeding the machine. 🔧
🪦 CISA Orders Federal Agencies to Decommission 2,300+ End-of-Support Edge Devices Per Agency Within 12 Months: $500M Threat Intel Investment Aims to Cut Ransomware Entry Points by Half
Your tax dollars at work: $500M to learn that ancient routers are bad. Actually ancient. Like, "still running firmware from the Obama era" ancient. CISA just ordered feds to yeet 2,300+ zombie edge devices per agency—firewalls, VPNs, IoT sensors, whatever that smartwatch your CISO's nephew plugged in. 21% of ransomware starts here. 30% of agencies even know what they own. The rest? Excel spreadsheets and prayer. 🪦 Federal IT: where "continuous discovery" is a 24-month aspirational goal and your PII is the collateral damage. Who's betting your state's DMV still has a Cisco from 2014?
Federal agencies have spent years treating edge devices like that one drawer everyone pretends doesn't exist—full of mystery cables, a 2012 Cisco router, and existential dread. CISA's Binding Operational Directive 26-02, dropped February 5, says the party's over: inventory every unsupported IoT gizmo, VPN box, and firewall fossil within 90 days, then yeet them into the sun within 12 months. The 18-month hard stop for stragglers? That's your "we're not kidding" deadline.
How this actually works
Agencies must catalog anything terminating external traffic—routers, load balancers, that "smart" coffee maker someone plugged into the guest VLAN. If vendor support died, it dies too. Patchable devices get 3 months grace; everything else gets decommissioned or replaced. Continuous discovery becomes mandatory by February 2028, because CISA knows this garbage regenerates like a horror-movie monster.
What happens when you don't
- Exploitation: 21% of 2025 ransomware incidents started at the edge—state actors and crime syndicates love unpatched firmware like raccoons love unsecured trash
- Lateral movement: One dead router becomes a highway for credential theft and classified data exfiltration
- Compliance pain: GAO already found 7 high-severity vulnerabilities in 4 legacy systems; imagine that multiplied across ~100 agencies
The institutional response (and where it wobbles)
| Strength | Gap |
|---|---|
| $500M threat-intel subscription to Recorded Future | Only ~30% of agencies submitted preliminary inventories |
| Automated discovery tools (RunZero, Shodan integration) | <10% actual decommissioning progress so far |
| OMB supplemental funding for hardware procurement | Manual spreadsheet warriors risking deadline extensions |
| Vendor liaison programs for migration paths | Bulk procurement contracts still pending execution |
The timeline nobody asked for but everyone's getting
- May 6, 2026: Inventory deadline—API-driven asset management separates adults from children
- August 2026: Patch-or-replace decision point for salvageable devices
- February 2027: 12-month decommissioning cliff—expect procurement chaos and vendor gold-rush pricing
- August 2027: Final EOS purge; ransomware groups pivot hard to whatever's left
- February 2028: Continuous discovery operational—≤30 day detection latency for newly expired assets
The bottom line
BOD 26-02 treats federal edge infrastructure like the attack surface it actually is: massive, poorly documented, and actively hunted. Early movers get reduced breach probability; laggards get to explain to Congress why a 2019 VPN concentrator just became a Chinese APT's favorite doorway. The 21% → <10% ransomware vector projection only holds if agencies treat this like operational necessity, not compliance theater. 🔥
In Other News
- University of Mississippi Medical Center hit by ransomware attack, shutting down systems and canceling procedures
- ShinyHunters cybergroup steals 800,000+ employee records from Wynn Resorts via Oracle PeopleSoft vulnerability, demands $1.5M in Bitcoin
- U.S. Coast Guard Deploys PRATUS on Microsoft Azure Government for Enterprise Incident Command, Replacing Legacy IMSS System
- Discord delays global teen age verification rollout to second half 2026 after 70,000+ user ID photos leaked by Persona vendor


Comments ()