$9M Breach: AI Script Kiddies Weaponize Default FortiGate Passwords in Enterprise Slaughter

TL;DR
- Hellcat group exfiltrated 44GB of sensitive data from Ascom’s ticketing system via AI-compromised FortiGate devices
- Let’s Encrypt adopts DNS-PERSIST-01 for wildcard certificate issuance with reusable validation records
- Google Blocks 255,000 Apps from Play Store in 2025 for Excessive Sensitive Data Access, Bans 80,000 Developer Accounts
🤖 44GB Breach: AI-Powered Hellcat Group Weaponizes LLMs Against 500 FortiGate Firewalls
500 FortiGates, 44GB of Jira sludge, and two LLMs doing the hacker's homework. Hellcat didn't breach Ascom—they outsourced the breach to ChatGPT's evil twin. Default passwords + AI script kiddies = your roadmap to $9M pain. When your firewall management needs MFA more than your Netflix account, we've failed. How many of your 'secure' appliances are just waiting for their AI-assisted eulogy?
FortiGate devices—supposedly the wall between your network and the abyss—just became the delivery mechanism for 44GB of stolen credentials. Hellcat didn't breach Ascom's Jira system by outsmarting security researchers. They asked ChatGPT for help. Twice.
How the Machine Learned to Betray You
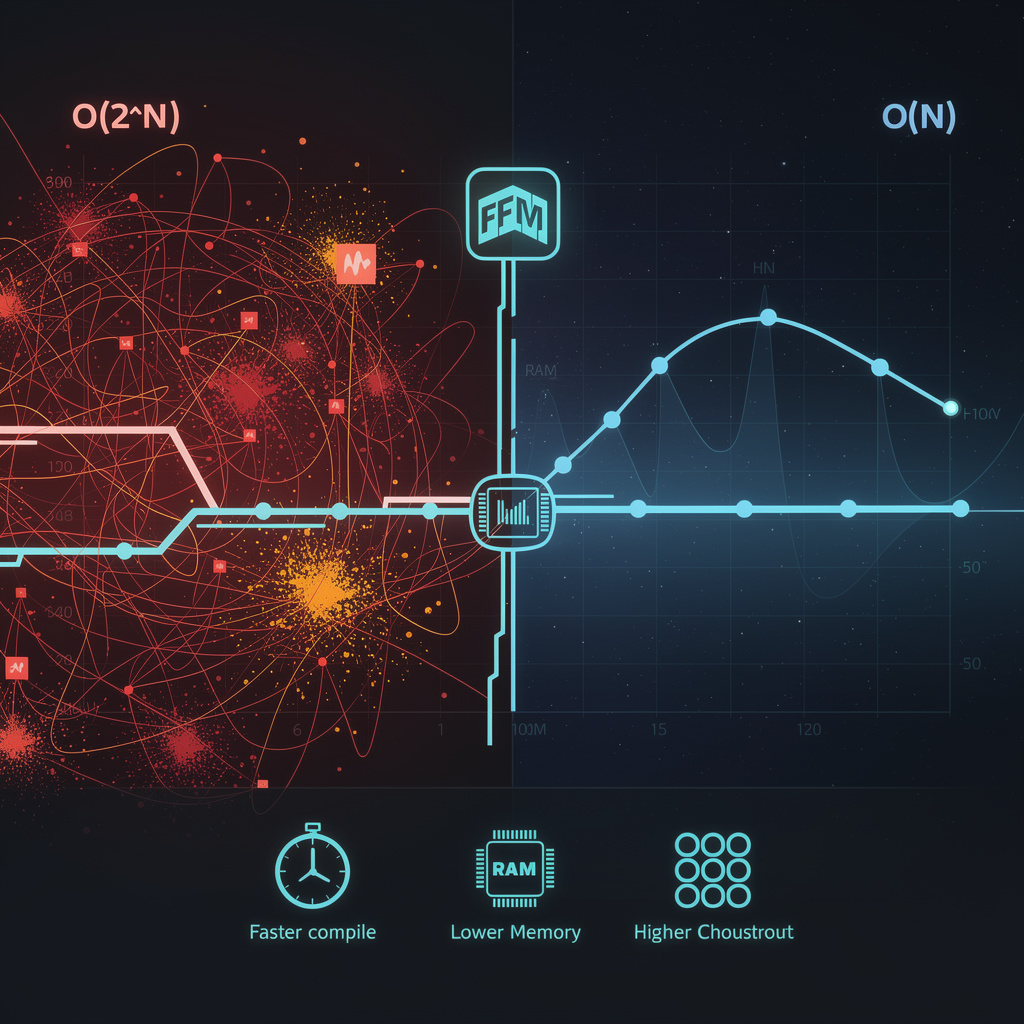
The attack chain reads like a corporate IT horror story written by someone who actually understands Kerberos. Hellcat found ~500 FortiGate firewalls with management interfaces flapping in the breeze—default credentials, no MFA, basically a "please rob me" sign. Then they did something new: they fed network topology into commercial LLMs and got back PowerShell payloads optimized for the victim's specific VLAN layout. One AI generated attack scripts. Another supplied real-time exploitation code. Human creativity replaced by API calls.
The timeline is almost insulting in its efficiency:
- ~January 2026: Initial FortiGate compromise via credential stuffing
- Early February: AI "assembly line" produces tailored payloads
- February 10: Lateral movement via pass-the-hash and DCSync—Mimikatz doing what Mimikatz does
- February 15: Custom infostealer injected into Jira process, 44GB extracted
- February 22: Exfiltration complete, public disclosure, frantic patching
Three million bytes per minute to an Azure blob. Your cloud bill probably looks worse.
What Actually Hurts
- Credential exposure: 2.1 million users linked to Ascom's ticketing system—field engineers, partners, anyone who opened a support ticket
- Downstream risk: OAuth tokens and API keys enable replay attacks against SaaS dependencies
- Business impact: $7–9 million estimated damage, mostly from leaked product roadmaps and the inevitable compliance theater to follow
The Patch Parade Nobody Asked For
Emergency fixes dropped for BeyondTrust RCE, Ivanti EPMM zero-day, Splunk's "Secure Indexer," Windows Admin Center privilege escalation, and Chrome CVE-2026-2441. Five vendors. One breach. The patch-gap window isn't a vulnerability—it's a business model.
What Happens Next
- 0–30 days: Forensic scans find another ~150 compromised FortiGates; Fortinet ships firmware updates that somehow don't address the "we exposed management interfaces" problem
- 30–180 days: Regulators discover AI exists; NIST drafts mandatory risk assessments while enterprises adopt "AI-attack surface" as their new favorite meaningless phrase
- ≥6 months: Zero-trust firewalls with "AI-behavior analytics" become the upsell; cyber-insurance premiums spike for anyone admitting they use LLMs in production
The real punchline? Hellcat didn't exploit a zero-day in the LLMs. They paid for API access like any other SaaS customer. When your threat actor has better AI governance than your SOC, the game isn't rigged—it's just over.
🏴☠️ DNS-PERSIST‑01: Single TXT Record Now Unlocks Unlimited Wildcard Certs—DNS Write Access Becomes Critical Attack Surface
One TXT record to rule them all: Let’s Encrypt’s DNS-PERSIST‑01 lets you set-and-forget a single token for unlimited wildcards. 🏴☠️ That’s 90 days of "convenience" with DNS write access as your new crown jewels. Miss thepersistUntil? Congrats, your infra now has eternal life—whether you want it or not. DevOps teams celebrating fewer API calls; red teams celebrating fatter targets. Who’s auditing your_acme-challengezone today? — Would you trust your wildcard certs to a single TXT record, or is this just DNS-01 with extra existential dread?
Let’s Encrypt just deployed DNS-PERSIST-01, and it's exactly what you'd expect when engineers optimize for their own pain while sleepwalking into someone else's nightmare. One TXT record. Infinite certificates. What could go wrong?
How this actually works (and why your DNS admin just became your single point of failure)
Traditional DNS-01 validation makes you publish a fresh TXT record every 90 days—annoying, error-prone, but distributed failure. DNS-PERSIST-01 lets you park one token under _acme-challenge.<domain> with an optional persistUntil timestamp, then mint wildcards and single-host certs until that date without touching your DNS provider again.
The mechanics are elegant poison: Base64URL token, ISO-8601 expiration, parallel TXT records for concurrent issuance. Latency drops from propagation hell to near-zero. Automation pipelines rejoice. And your DNS credentials? Now they're a persistent certificate factory for anyone who nabs them.
The security "implications" (read: concentrated catastrophe)
DNS write access: Compromise → unlimited wildcard issuance for the duration. No rate limits. No re-validation. Just *.yourdomain.com served fresh to whoever owns your API keys.
Token reuse: Fewer moving parts, single catastrophic failure mode. Classic engineering tradeoff.
Authorization lifetime: Skip persistUntil and you get indefinite reuse, subject to "CA-policy limits" that nobody reads until after the breach.
Wildcard expansion: One record covers everything. Blast radius? Maximum.
Operational simplicity: Actually real. CI/CD teams will adopt this before security reviews finish their coffee.
Timeline of consequences
- Late Q1 2026: Staging opens. Early adopters discover
persistUntilparsing bugs in three languages. - Q2 2026: Production goes live. Two weeks later, first incident: "We rotated our DNS API key but forgot the persistent record existed."
- 2026–2027: CDNs and SaaS platforms migrate en masse. Mean time to certificate issuance drops 80%. Mean time to incident response for DNS compromise? Ask again later.
- 2028+: Someone proposes "credential-bound DNS records" as a new standard, solving the problem we just created.
The mitigation list nobody will follow completely
Restrict DNS write access. Set finite persistUntil. Monitor TXT records. Rotate tokens. Audit wildcard usage. These are correct. They are also additional work that undermines the operational savings that make DNS-PERSIST-01 attractive in the first place. Organizations will implement 2 of 5, declare victory, and move on.
Let’s Encrypt has built something genuinely useful for operators running certificate farms at scale. They've also demonstrated that "secure by default" and "convenient for power users" remain mutually exclusive when the default is indefinite persistence. The IETF draft process approved this. Your threat model may vary.
🎪 1.75M Apps Blocked: Google's AI Enforcement Surges While 72% of AI Apps Leak Cloud Secrets
1.75M apps yeeted into the void but 72% of AI apps still waving hardcoded cloud creds like a neon 'HACK ME' sign 🎪 Google's AI bouncer blocked 255k data-hungry apps while 27M malware gremlins party in sideload alley — your 'secure' Play Store is basically a velvet rope with a broken lock. EU regulators circling like sharks with DMA subpoenas while devs keep shipping secrets in plaintext. Who's actually winning here? — When did your phone's app store become a compliance theater with better marketing?
255,000 apps just got yeeted off the Play Store for demanding your camera, contacts, and location like entitled exes. Another 80,000 developer accounts? Permabanned. The reason: they were building data-harvesting nightmares disguised as flashlight apps and crypto wallets. Painful? Only if you enjoyed having your digital life strip-mined by randos in basements.
How the machine actually eats its young
Google's enforcement runs on three brutal engines:
- Play Protect scans 350 billion app instances daily — static analysis, dynamic execution, behavioral anomalies. Anything that phones home weirdly gets flagged.
- Gemini-powered classifiers surface suspicious code patterns — hardcoded secrets, obfuscated payloads, permission overreach that smells like fraud.
- Mandatory identity verification and pre-review checks now gatekeep new accounts, while the Play Integrity API performs 20 billion daily integrity checks.
The 255,000 data-access blocks specifically target apps requesting sensitive permissions without justification. The 80,000 account bans represent a ~57% spike in developer expulsions year-over-year.
What broke, what bled, what Google won't fix
Data exposure: 255,000 apps blocked → unknown millions of potential breaches prevented, though Google doesn't quantify user impact directly.
Financial fraud: 20 crypto-wallet impersonators identified by Cyble Research in January 2026 were among the intercepted batch, indicating focused targeting of financial scams.
Ecosystem rot: 27 million malicious apps now circulate outside Play Store, up from 13 million in 2021. The moat's holding; the wilderness is burning.
Hardcoded secrets: ~72% of AI-related Play Store apps still leak Google Cloud credentials — a vulnerability class untouched by 2025 enforcement.
The timeline nobody asked for
- 2025: 1.75 million policy violations blocked (down 25% YoY), 160 million fake reviews removed, 266 million risky installs intercepted
- 2026–2027: Projected 10–15% further reduction in policy violations as AI review precision improves; "bad developer" bans stabilize at 80–90k annually
- 2028–2030: Mandatory secret-scanning and encrypted storage checks could cut hardcoded credential prevalence 30%; polymorphic malware (e.g., TrustBastion variants) demands continuous model retraining
Google's enforcement model now sets the de facto industry standard. Competing stores face pressure to match AI-driven pipelines; regulators reference these metrics when drafting digital-market legislation. The 25% drop in total violations correlates directly with AI-assisted review rollout — causation, not coincidence.
But here's the real joke: 27 million malicious apps thrive in sideloading wilderness while Google polishes its storefront trophy. The castle's secure. The village outside? 🔥
In Other News
- UK stalking reports surged 896% since 2018 as AirTags and GPS trackers enable tech-facilitated abuse
- Laravel 12+ Hyro RBAC system launches with zero-config enterprise-grade authorization and audit logging


Comments ()